After all the interesting things I have been reading lately about wifi sd cards, and my never ending interest in tiny embedded devices/hacking things that were made for one purpose and using them for some other purpose.. I figured I should pick one up and see what was going on. So I perused one of my favorite auction sites, and found  some Toshiba Flashair wifi sd cards going for around $20, so I tossed a few bids out, and ended up winning one for under $22 shipped. Later to find out in my further investigation that I had jumped the gun, and that the Flashair cards do not run Linux, but instead a proprietary OS.. unlike the Transcend, Flucard, and PQI Air. That however did not deter me from looking, who knows what still could be done..
some Toshiba Flashair wifi sd cards going for around $20, so I tossed a few bids out, and ended up winning one for under $22 shipped. Later to find out in my further investigation that I had jumped the gun, and that the Flashair cards do not run Linux, but instead a proprietary OS.. unlike the Transcend, Flucard, and PQI Air. That however did not deter me from looking, who knows what still could be done..
After receiving the card I took a look at the website and saw a firmware update utility (FAFWUpdateTool_v10004) and from my previous research this was possibly the key to figuring out more to this device. So I installed it and read through the documentation provided on the site.
Before actually running the utility however I figured I would look at the card as it opens on my Windows 8.1 laptop.
The first thing that I noticed was that it was formatted in FAT32 and it looked like your regular sd card, with one exception.. some hidden folders.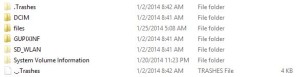
Particularly the hidden one named “SD WLAN”, which once opened had one file that really intrigued me, the “CONFIG” file. After opening it up I noticed there were many options and after Googling, many more Official Here and More Here. So I went about editing it to see what would happen. I wanted it to connect as a client on my network, so I didn’t have to connect to it, as the default setting is access point, so I changed APPMODE to 5, changed APPSSID to match mine, and changed APPNETWORKKEY to also match. Next, I found that the unofficial sources stated that there was also a COMMAND function, so I figured “help” might be a good start. I then left everything else alone, then saved and safely removed and reinserted.
My config file looked like the following:
CIPATH=/DCIM/100__TSB/FA000001.JPG
APPMODE=5
APPSSID=MYNETWORKSSID
APPNETWORKKEY=NETWORKKEY
VERSION=F24A6W3AW1.00.04
CID=02544d53573038470750031fac00cc01
PRODUCT=FlashAir
VENDOR=TOSHIBA
COMMAND=help
*note that network key will automatically be *’d out on reboot of card.
After rebooting the card I noticed it showed up on my network, at this point I accessed its web page and was greeted
with the webpage, which was useless.. I wanted to know where the command output was being written to, after digging through the files, I went back to Google, which led me back to the unofficial link above for extrud3d.com (thanks for your help guys).
Anyways, after navigating to /IPADDRESSOFFLASHAIR/eva.cgi, I was presented with a list of the commands:
> help
help show help
version show version
mod Modify Memory
dump Dump Memory
stat show status
ip Address Setting
ping ping
reboot reboot system
macsend MAC frame send
setup TELEC command
send TELEC command
stop TELEC command
show TELEC command
deauth deauth command
print console output
srom SPI ROM access
sleep sleep setting
fat file system
wlan Wireless LAN control
dhcpd DHCP server
dhcpc DHCP client
nbios NetBios service
wps Wi-Fi Protected Setup
sd SD Card Access
http HTTP Client
httpd HTTP Daemon
rfic set RF-IC serial data rfic
iperf Measuring performance
sysclk change System clk
ps ps [on/off]
pw pw
pio pio
netlog log
d
followed by what looked like a startup log. Now I was getting somewhere..
So I tried a number of the commands, but I had little luck here and there as they appeared to be very limited as I could not see what the arguments/flags were as appending “-h” or “?” almost never returned anything. It is also a pain because you have to edit the CONFIG file, save, safely remove, pull out, put back in, wait for it to reconnect to the network, then refresh the page each time you want to run a command.
From the interesting ones above, what I could get to run and ascertain:
help command showed the above commands.
version command printed version information.
mod command appeared to be a write function. (I believe this and dump is to some flash storage because it returned all 0’s)
dump command returned what appeared to be memory addresses and lengths followed by raw binary output.
stat command returned wlan stats, like signal strength, rx and tx packets etc.
ip command appeared it was to setup ipaddress settings.
ping command pinged address in argument.
fat can do mkdir, cp commands etc, so it is access to the sd card flash system.
all the other ones for the most part required arguments and/or flags that I did not know or returned nothing..
Next thing to do was update the firmware and see what would happen, just as I had researched it added a file which gets deleted on reboot (so I pulled it out) which is called “fwupdate.fbn”. It also appears that it edits the config file to run the update on reboot “sd update fwupdate.fbn -nomount”. Just out of curiousity I decided to take a look at the file in Hex editor, and just as I had heard in my research there was straight ascii text showing the commands, some of which were not shown in the help command or anywhere else for that matter.
Here is the file fwupdate.zip
I also managed to get a few more commands to run as the flags where listed on some, but I still did not see how to get any good access to the embedded system, or run any custom code on the card.. The one that really interested me was the setting the device to developer mode:
COMMAND=level 1048
But it only returned “developer” in the log, no new ports opened up, and nothing changed as far as I could see.
I was hoping to get the rf-ic figured out, but I could not get it to work or even find documentation on it anywhere.
Since there was a developer site for the flashair, I did browse around and see that there were options to pay a company to build custom cgi code for the flashair, so I figured I would email Toshiba through thier contact link to see if they might be willing to provide the tool for students, but I never heard back..
With my resources exhausted, I tryed to run binwalk on the fbn file, but it was not able to find anything.. I think they might be flipping some bytes to hide the true file format, but I have not figured it out. I do know there very well could be good stuff in there if someone can crack it.
The next step would be to cut the card open, and first see what chipset it uses (I could note find it anywhere) and
second try to dump the flash and run ida on it.. both of which I probably won’t be able to do anytime soon. But perhaps someone out there has the tools to do so? If I do, you can guarantee I will post it here for everyone to see.
**Update I did some more research and found some images of the board digging through google image search..

Chips are as follow:
Processor : TC90636XBG ?
Flash Memory : TC58NVG6D2GLAD0E ?
WIFI : AIROHA AL2238 wifi b/g
I cannot read the others, but either way I was not able to find any details about the Processor or even the Flash Memory.
Also, with the help of a friend, I ran the update file through IDA Pro, and he said it appears IDA is detecting it as Armv6 code. We were not able to find the bootloaders load start. Although it may not be in the update file. More is still needed to be researched, but I wanted to update this.

Just picked up one of these things – they now let you use lua scripts to extend it directly, although the api they provide isn’t the best (and nor is its documentation…)
Awesome! I love these things. There should be a serial interface available directly to the controller. Usually the controller is ARM M3 based. You need a microscope to see more, so that we can determine the chips. Also check out Bunnies blog about SD card hacking.
http://www.bunniestudios.com/blog/?p=3554
Thanks E:V:A that is very interesting.
Nevermind. No luck.
Just got one. Any luck yet? You tried shellshock on it?
I don’t think that it runs Linux, so I doubt it is susceptible to the bash bug..
Let me know if you find any security flaws though.. I have yet to do much messing around with it lately.
The version w-02 looks a bit different inside,
http://imgur.com/a/bqSj5
And I think you got the processor identifier wrong, it should be TC90535XBG
Thanks for the info Nicklas, have you had any luck with these cards?